
The 10 Best Futon Beds Reivews
FUTONS WERE—and are—staple furniture of broke college kids everywhere. The old-school wood-slat frames and heavy,…

FUTONS WERE—and are—staple furniture of broke college kids everywhere. The old-school wood-slat frames and heavy, lumpy mattresses were designed entirely with versatility in mind: Couch by day, bed by night. And, above all else, they were extremely affordable. We’re talking $200 or less for a halfway decent model, including the frame and mattress. Maybe less…

In these uncertain times preserving food has become one of the easiest ways to make sure that healthy and nutritious meals are always available. Buying the best stainless steel food dehydrator is one of the easiest (and most fun) ways to create dehydrated snacks and main meal ingredients. But there’s another reason aside from having…

Customer Reviews: 1. I bought this bathtub mat for my granddaughter and we both love it! The bathmat is made of quality material and is very easy to wash. The best non slip bath mat for baby was very easily suctioned to the bathtub floor. My granddaughter loves the colors of the bathmat and loves…

Moon lamp appear the same like the moon the reason being they’re designed using a 3D printing technology which display every feature of the moon. Moon lamps are rechargeable and cordless, which means you are not required to charge them when they’re lighting. These lamps produce soft light that help to promote sleeping. In addition,…
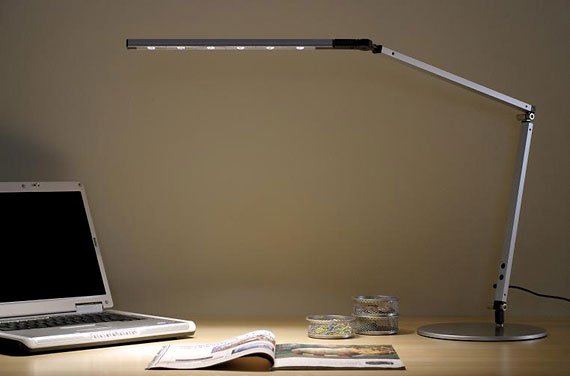
Buying a new desk lamp is a very popular way for people to improve the environment in our home office without spending a fortune. Not only will an improved desk lamp provide a higher quality of light, but also make your office space look and feel nicer making it a better place to spend some…
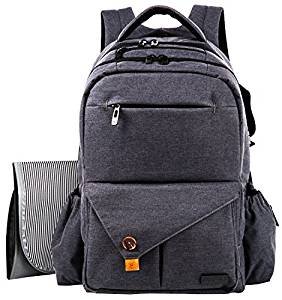
When you are on the go with your baby, that diaper bag is your livelihood. Without the right things on you, your trip is cut short and it is back to home base. You definitely don’t want to find yourself stuck out and about with the right supplies. You want to carry everything you need…

If there’s one musical instrument that has truly withstood the test of time, it’s the piano. You can find beautiful piano music from two or three hundred years ago, and it sounds just as good now as it did then. Millions of people across the world enjoy playing the piano, and many more enjoy simply…

Your kids are a source of joy for every parent out there. We want them to be happy because they make our life a joy. Well, we also need to give our kids amazing gifts so they can feel happy as soon as possible. And some child safe night lights can do the job. We…

Hey, Dads: this guide is for you. We’ll show you why it’s totally fine for you to wear a diaper bag/backpack as you’re toting you’re little one around, and why the form, function and appearance of your bag are important. 1.Graco Gotham Smart Organizer System Back Pack Diaper Bag Buying the perfect large diaper bag…

Some of the things to consider when deciding which lamp is best for your needs are brightness and ability to control lighting levels. You want to determine if you need multiple settings for detailed drawings and for different mediums, adjustability so that you can position the light exactly where you need it, and glare reduction….